How to Configure GRE VPN
Introduction
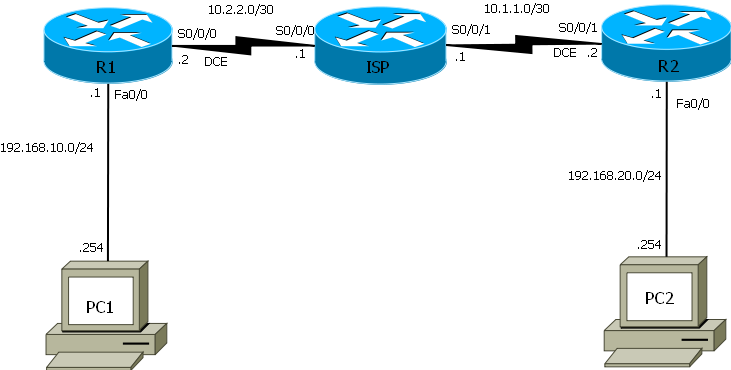
This network create a VPN tunnel between R1 and R2 using GRE tunneling protocol that can encapsulate a wide variety of protocol packet types inside IP tunnels. GRE creates a virtual point-to-point link to Cisco routers at remote points over an IP internetwork. Routing protocols can be used over a GRE tunnel just as though it were a point to point circuit.
Prepare the Network and Basic Configurations
- Cable the network according the topology diagram.
- Clear existing configurations on the routers.
- Perform basic router configuration.
Configure Router and GRE Tunnel Interfaces
- Configure R1, R2 and ISP routers with IP addresses and masks.
R1#configure terminal R1(config)#interface f0/0 R1(config-if)#ip address 192.168.10.1 255.255.255.0 R1(config-if)#no shut R1(config-if)#
R1(config)#interface s0/0/0 R1(config-if)#ip address 10.2.2.2 255.255.255.252 R1(config-if)#no shutdown R1(config-if)#
R2#configure terminal R2(config)#int s0/0/1 R2(config-if)#ip address 10.1.1.2 255.255.255.252 R2(config-if)#no shut R2(config-if)#
R2(config-if)#int f0/0 R2(config-if)#ip address 192.168.20.1 255.255.255.0 R2(config-if)#no shut R2(config-if)#end R2#
ISP#configure terminal ISP(config)#interface s0/0/0 ISP(config-if)#ip address 10.2.2.1 255.255.255.252 ISP(config-if)#no shutdown ISP(config-if)#
ISP(config-if)#inte s0/0/1 ISP(config-if)#ip address 10.1.1.1 255.255.255.252 ISP(config-if)#no shut ISP(config-if)#end ISP#
- Configure PC1 and PC2 with IP address and default gateway.
- Configure GRE Tunnel interface on R1 and R2
R1(config)#interface tunnel 0 R1(config-if)#description GRE-Tunnel to R2 R1(config-if)#ip address 192.168.1.1 255.255.255.252
R1(config-if)#tunnel source 10.2.2.2 R1(config-if)#tunnel destination 10.1.1.2 R1(config-if)#end
Tunnel source is R1’s serial 0/0/0 interface and tunnel destination is R2’s serial 0/0/1 interface.
R2(config)#interface tunnel 0 R2(config-if)#description GRE-Tunnel to R1 R2(config-if)#ip address 192.168.1.2 255.255.255.252
R2(config-if)#tunnel source 10.1.1.2 R2(config-if)#tunnel destination 10.2.2.2 R2(config-if)#end
Tunnel source is R2’s serial 0/0/1 interface and tunnel destination is R1’s serial 0/0/0 interface.
Enable EIGRP with process ID 1 on R1 and R2
- Advertise the LAN interface Fa0/0 and the tunnel interfaces on both R1 and R2. Do not advertise to ISP router.
R1(config)#router eigrp 1 R1(config-router)#no auto-summary R1(config-router)#network 192.168.1.0 0.0.0.3 R1(config-router)#network 192.168.10.0 0.0.0.255 R1(config-router)#end
R2#conf ter R2(config)#router eigrp 1 R2(config-router)#no auto-summary R2(config-router)#network 192.168.20.0 R2(config-router)#network 192.168.1.0 0.0.0.3 R2(config-router)#end
- Apply default route on R1 and R2
R1(config)#ip route 0.0.0.0 0.0.0.0 s0/0/0 R2(config)#ip route 0.0.0.0 0.0.0.0 s0/0/0
Before you configure authentication and encryption test that the network is working as planned. So that you will know what to troubleshoot incase you encounter a problem at the end and It is easier to troubleshootin before you apply authentication and encryption.
- Check the interfaces on R1, R2, and ISP routers using show ip interface brief command.
R2#show ip int brief
Interface IP-Address OK? Method Status Protocol FastEthernet0/0 192.168.20.1 YES manual up up FastEthernet0/1 unassigned YES unset administratively down down Serial0/0/0 unassigned YES unset administratively down down Serial0/0/1 10.1.1.2 YES manual up up Tunnel0 192.168.1.2 YES manual up up
- Use show ip route command to check the routing table on R1 and R2.
R1#show ip route
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Gateway of last resort is 10.2.2.1 to network 0.0.0.0
C 192.168.10.0/24 is directly connected, FastEthernet0/0
D 192.168.20.0/24 [90/26882560] via 192.168.1.2, 00:01:33, Tunnel0
10.0.0.0/30 is subnetted, 1 subnets
C 10.2.2.0 is directly connected, Serial0/0/0
192.168.1.0/30 is subnetted, 1 subnets
C 192.168.1.0 is directly connected, Tunnel0
S* 0.0.0.0/0 [1/0] via 10.2.2.1
- Test connectivity using ping command between PC1 and PC2 or use extended ping from R1 LAN interface Fa0/0 to R2 LAN interface and vice-versa.
R2#ping ip Target IP address: 192.168.10.1 Repeat count [5]: Datagram size [100]: Timeout in seconds [2]: Extended commands [n]: y Source address or interface: 192.168.20.1 Type of service [0]: Set DF bit in IP header? [no]: Validate reply data? [no]: Data pattern [0xABCD]: Loose, Strict, Record, Timestamp, Verbose[none]: Sweep range of sizes [n]: Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.10.1, timeout is 2 seconds: Packet sent with a source address of 192.168.20.1 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 36/36/36 ms
IPsec Encryption and Authentication
- Configure an Internet Security Association and Key Management Protocol (ISAKMP) policy, an ISAKMP key, and an IPSec transform set. The ISAKMP policy, key, and IPSec transform set must match on both sides of a single tunnel.
R1(config)#crypto isakmp policy 1 R1(config-isakmp)#authentication pre-share R1(config-isakmp)#group 5 R1(config-isakmp)#encryption aes R1(config-isakmp)#hash sha R1(config-isakmp)#exit
R1(config)#crypto isakmp key 0 blindhog address 10.1.1.2
R1(config)#crypto ipsec transform-set aes-sha esp-aes esp-sha-hmac
- Extended access control list that permit ip only from R2 serial 0/0/1 to R1 serial 0/0/0 interface.
R1(config)#access-list 101 permit GRE host 10.2.2.2 host 10.1.1.2
- Configure the crypto map on R1
R1(config)#crypto map vpn 11 ipsec-isakmp
% NOTE: This new crypto map will remain disabled until a peer
and a valid access list have been configured.
R1(config-crypto-map)#description VPN from R1 to R2
R1(config-crypto-map)#set peer 10.1.1.2
R1(config-crypto-map)#set transform-set aes-sha R1(config-crypto-map)#match add 101 R1(config-crypto-map)#exit
R1(config)#int s0/0/0 R1(config-if)#crypto map vpn R1(config-if)#end R1#
R2(config)#crypto isakmp policy 1 R2(config-isakmp)#authentication pre-sha R2(config-isakmp)#group 5 R2(config-isakmp)#encryption aes R2(config-isakmp)#hash sha R2(config-isakmp)#exit
R2(config)#crypto isakmp key 0 blindhog address 10.2.2.2
R2(config)#crypto ipsec transform-set aes-sha esp-aes esp-sha-hmac R2(cfg-crypto-trans)#exit
- Extended access control list that permit ip only from R1 serial 0/0/0 to R2 serial 0/0/1 interface.
R2(config)#access-list 102 permit GRE host 10.1.1.2 host 10.2.2.2
- Configure the crypto map on R2
R2(config)#crypto map vpn 12 ipsec-isakmp
% NOTE: This new crypto map will remain disabled until a peer
and a valid access list have been configured.
R2(config-crypto-map)#description VPN from R2 to R1
R2(config-crypto-map)#set peer 10.2.2.2
R2(config-crypto-map)#set transform-set aes-sha R2(config-crypto-map)#match add 102 R2(config-crypto-map)#exit
R2(config)#int s0/0/1 R2(config-if)#crypto map vpn
R2(config-if)#end
Test and Verify VPN Connectivity
- Use show ip route command on R1 to check that a route exist to 192.168.20.0/24 network through the tunnel interface. Do the same on R2 to verify that a route exist to 192.168.10.0/24 network through the tunnel interface.
R2#show ip route
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Gateway of last resort is 10.1.1.1 to network 0.0.0.0
D 192.168.10.0/24 [90/26882560] via 192.168.1.1, 00:13:17, Tunnel0
C 192.168.20.0/24 is directly connected, FastEthernet0/0
10.0.0.0/30 is subnetted, 1 subnets
C 10.1.1.0 is directly connected, Serial0/0/1
192.168.1.0/30 is subnetted, 1 subnets
C 192.168.1.0 is directly connected, Tunnel0
S* 0.0.0.0/0 [1/0] via 10.1.1.1
- Use ping or extended ping command to test connectivity between 192.168.10.0/24 and 192.168.20.0/24 network.
R1#ping ip
Target IP address: 192.168.20.1 Repeat count [5]: Datagram size [100]: Timeout in seconds [2]: Extended commands [n]: y Source address or interface: 192.168.10.1 Type of service [0]: Set DF bit in IP header? [no]: Validate reply data? [no]: Data pattern [0xABCD]: Loose, Strict, Record, Timestamp, Verbose[none]: Sweep range of sizes [n]: Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.20.1, timeout is 2 seconds: Packet sent with a source address of 192.168.10.1 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 36/36/36 ms
- Use show crypto engine connections active, show crypto map and show crypto ipsec sa command s to verify connection.
R2#show crypto engine connections active Crypto Engine Connections ID Type Algorithm Encrypt Decrypt IP-Address
1 IPsec AES+SHA 0 81 10.1.1.2 2 IPsec AES+SHA 82 0 10.1.1.2 2001 IKE SHA+AES 0 0 10.1.1.2
R2# show crypto map
Crypto Map "vpn" 12 ipsec-isakmp
Description: VPN from R2 to R1
Peer = 10.2.2.2
Extended IP access list 102
access-list 102 permit gre host 10.1.1.2 host 10.2.2.2
Current peer: 10.2.2.2
Security association lifetime: 4608000 kilobytes/3600 seconds
Responder-Only (Y/N): N
PFS (Y/N): N
Transform sets={
aes-sha: { esp-aes esp-sha-hmac } ,
}
Interfaces using crypto map vpn:
Serial0/0/1
R2#show crypto ipsec sa
interface: Serial0/0/1
Crypto map tag: vpn, local addr 10.1.1.2
protected vrf: (none)
local ident (addr/mask/prot/port): (10.1.1.2/255.255.255.255/47/0)
remote ident (addr/mask/prot/port): (10.2.2.2/255.255.255.255/47/0)
current_peer 10.2.2.2 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 304, #pkts encrypt: 304, #pkts digest: 304
#pkts decaps: 302, #pkts decrypt: 302, #pkts verify: 302
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 168, #recv errors 0
local crypto endpt.: 10.1.1.2, remote crypto endpt.: 10.2.2.2
path mtu 1500, ip mtu 1500, ip mtu idb Serial0/0/1
current outbound spi: 0x192C42F5(422331125)
PFS (Y/N): N, DH group: none
inbound esp sas:
spi: 0xF0333FAE(4029890478)
transform: esp-aes esp-sha-hmac ,
in use settings ={Tunnel, }
conn id: 1, flow_id: AIM-VPN/SSL-1:1, sibling_flags 80000046, crypto map: v
sa timing: remaining key lifetime (k/sec): (4473306/2869)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE
inbound ah sas:
inbound pcp sas:
outbound esp sas:
spi: 0x192C42F5(422331125)
transform: esp-aes esp-sha-hmac ,
in use settings ={Tunnel, }
conn id: 2, flow_id: AIM-VPN/SSL-1:2, sibling_flags 80000046, crypto map: v
sa timing: remaining key lifetime (k/sec): (4473305/2869)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE
outbound ah sas:
outbound pcp sas: