Modifying Permissions With ICACLS: Difference between revisions
No edit summary |
No edit summary |
||
| (16 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
*'''Purpose''' | *'''Purpose''' | ||
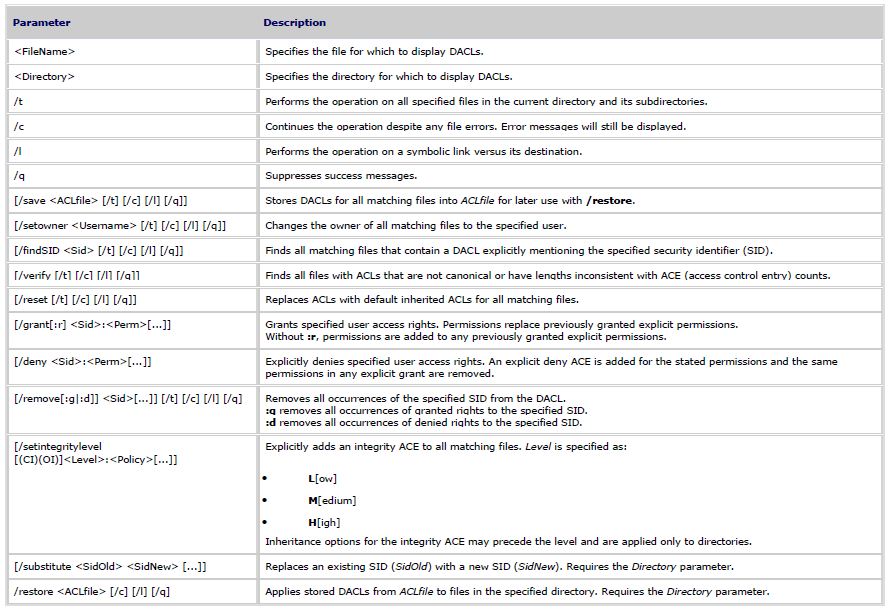
The ICACLS command displays or modifies discretionary access control lists (DACLs) on specified files or folders. It is also used to backup DACLs and apply stored DACLs to files in specified directories. This can be used with Windows Server 2008 Full edition and Server Core where no GUI exists. | |||
*'''Syntax''' | *'''Syntax''' | ||
| Line 9: | Line 8: | ||
[[File:Parameters.jpg]] | [[File:Parameters.jpg]] | ||
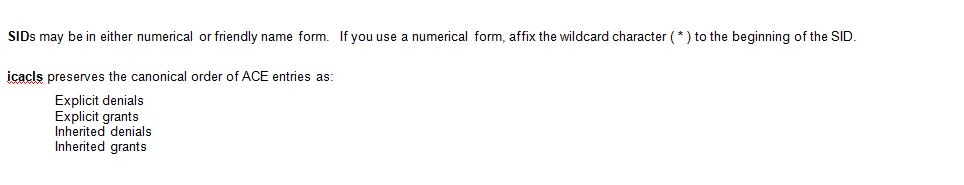
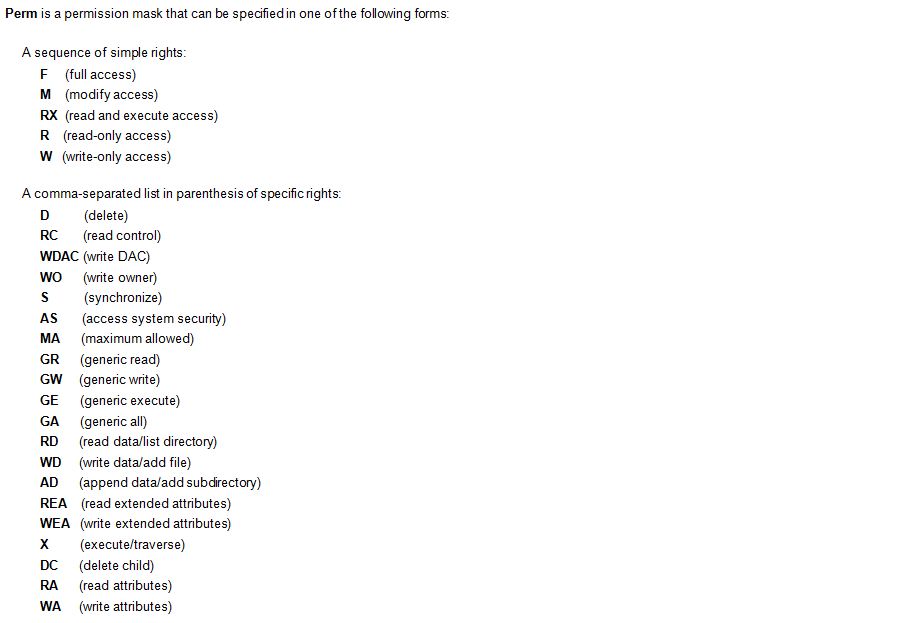
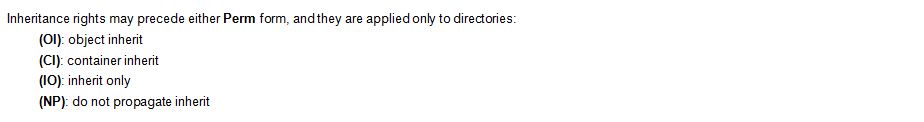
*'''Note:''' | |||
[[File:SIDs.JPG]] | |||
[[File:Perm.JPG]] | |||
[[File:Inherit.JPG]] | |||
*'''Examples:''' | |||
icacls c:\Directory1 | |||
- Will display the ACL listing the Users and Groups with permissions specified for the folder C:\Direcory1 | |||
icacls c:\Directory1 /Deny Users:M | |||
- Will deny the Users group Modify access to the folder C:\Directory1 | |||
icacls c:\windows\* /save AclFile /T | |||
- Will save the ACLs for all files under c:\windows and its subdirectories to AclFile. | |||
icacls c:\windows\ /restore AclFile | |||
- Will restore the Acls for every file within AclFile that exists in c:\windows and its subdirectories | |||
icacls file /grant Administrator:(D,WDAC) | |||
- Will grant the user Administrator Delete and Write DAC permissions to file | |||
icacls file /grant *S-1-1-0:(D,WDAC) | |||
- Will grant the user defined by sid S-1-1-0 Delete and Write DAC permissions to file | |||
Latest revision as of 22:12, 20 July 2010
- Purpose
The ICACLS command displays or modifies discretionary access control lists (DACLs) on specified files or folders. It is also used to backup DACLs and apply stored DACLs to files in specified directories. This can be used with Windows Server 2008 Full edition and Server Core where no GUI exists.
- Syntax
icacls <FileName> [/grant[:r] <Sid>:<Perm>[...]] [/deny <Sid>:<Perm>[...]] [/remove[:g|:d]] <Sid>[...]] [/t] [/c] [/l] [/q] [/setintegritylevel <Level>:<Policy>[...]]
icacls <Directory> [/substitute <SidOld> <SidNew> [...]] [/restore <ACLfile> [/c] [/l] [/q]]
- Note:
- Examples:
icacls c:\Directory1
- Will display the ACL listing the Users and Groups with permissions specified for the folder C:\Direcory1
icacls c:\Directory1 /Deny Users:M
- Will deny the Users group Modify access to the folder C:\Directory1
icacls c:\windows\* /save AclFile /T
- Will save the ACLs for all files under c:\windows and its subdirectories to AclFile.
icacls c:\windows\ /restore AclFile
- Will restore the Acls for every file within AclFile that exists in c:\windows and its subdirectories
icacls file /grant Administrator:(D,WDAC)
- Will grant the user Administrator Delete and Write DAC permissions to file
icacls file /grant *S-1-1-0:(D,WDAC)
- Will grant the user defined by sid S-1-1-0 Delete and Write DAC permissions to file